Top 5 Phishing Risks in Healthcare Emails
Post Summary
The five primary phishing risks in healthcare are general email phishing that exploits weak email protections, spear phishing that uses personal details to target specific individuals or departments, business email compromise that impersonates executives or vendors to redirect funds or data, QR code phishing that embeds malicious codes to bypass standard security filters, and AI-generated phishing that uses generative AI tools to produce polished and highly convincing attacks at scale.
General email phishing accounted for 63% of the 170 email-related breaches reported in healthcare in 2025, with 74% of affected domains lacking proper DMARC protection and Microsoft 365 breaches rising to 53% of incidents, up from 43% the prior year.
Spear phishing is especially dangerous in healthcare because attackers research specific targets and reference real colleagues, projects, and events to craft highly personalized messages, and cybercriminals now use AI to create deepfakes, forged IDs, and lifelike profile photos that make these attacks nearly impossible to distinguish from legitimate communications.
Business email compromise is a social engineering attack in which attackers impersonate executives, vendors, or legal advisors to manipulate organizations into transferring funds or sharing sensitive information, and healthcare is especially vulnerable due to complex payment systems, extensive third-party vendor relationships, and a workforce focused on patient care rather than fraud detection.
QR code phishing, also called quishing, embeds malicious QR codes in emails or physical materials that standard security systems cannot decode when they appear as images, redirecting users to credential-stealing sites or malware while bypassing the URL analysis that traditional email filters rely on.
Generative AI tools have enabled a 700% increase in credential phishing incidents in late 2024 by allowing attackers to produce polished, error-free phishing content at scale, mimic internal IT alerts and HR communications with precise organizational language, and continuously adapt tone and formatting to bypass security filters.
Phishing is a major cybersecurity threat in healthcare, with over 90% of cyber-attacks starting from phishing emails. In 2025 alone, phishing-related breaches exposed hundreds of thousands of patient records and cost organizations millions of dollars. Attackers use tactics like AI-generated messages, brand impersonation, and QR code scams to exploit vulnerabilities. Here's a quick breakdown of the top phishing risks healthcare organizations face:
Key takeaway: Healthcare organizations must strengthen defenses with multi-factor authentication, advanced email security tools, and staff training to combat these evolving threats. Solutions like DMARC enforcement and phishing simulations can significantly reduce risks.
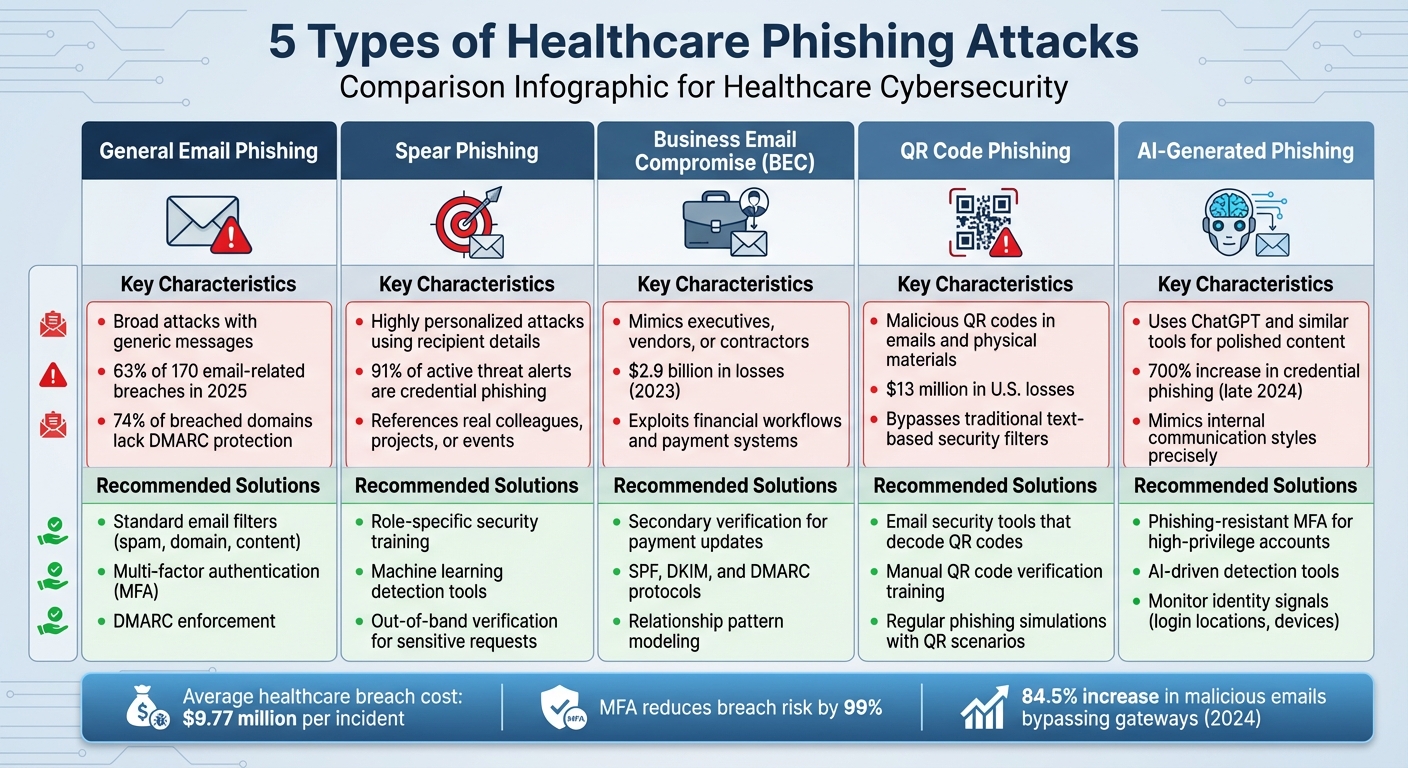
5 Types of Healthcare Phishing Attacks: Characteristics and Defense Strategies
Phishing Training for Healthcare Workers - HIPAA Certify
sbb-itb-535baee
1. General Email Phishing
General email phishing is the starting point for understanding more advanced phishing tactics and remains the most common method attackers use in healthcare cybersecurity.
How Common Is General Phishing?
General email phishing continues to dominate as the main entryway for healthcare cyberattacks. In 2025, it accounted for 63% of the 170 email-related breaches reported [2][8]. The problem has grown worse, with breaches on Microsoft 365 rising to 53% in 2025, compared to 43% in 2024 [2]. One major weakness? A staggering 74% of affected domains lacked proper DMARC protection, making it easy for attackers to spoof trusted email addresses [2].
The Toll on Healthcare Organizations
The widespread nature of phishing attacks has a ripple effect on healthcare operations. In 2025, mailbox takeovers caused by phishing made up 17% of email-related breaches but exposed over 630,000 patient records [2][3]. Once attackers gain access through stolen credentials, they can log in undetected and sift through historical emails for sensitive patient health information (PHI) [3]. To make matters worse, attackers often use high-pressure tactics, like fake IT alerts or supplier requests, to trick users into clicking malicious links [4]. These schemes have also evolved to exploit trusted platforms, such as direct secure messaging systems and Google-hosted services, making it even harder to spot identity abuse [3].
Financial and Data Breach Risks
The financial fallout from phishing-related breaches is staggering. On average, these incidents cost $7.4 million each. Breaches involving third-party vendor risk are slightly less costly at $4.9 million but can impact multiple organizations when vendor credentials are compromised [3]. The overall risk environment worsened in 2025, with 41% of healthcare organizations categorized as high risk, up from 31% in 2024 [2].
How to Fight Back Against Phishing
Given the financial stakes, effective defenses are a must. However, traditional approaches like user awareness training often fall short once credentials are stolen [3]. To stay ahead, organizations need to adopt email-layer security that blocks phishing attempts before they reach inboxes [3]. Strengthening DMARC enforcement is also critical, yet it's missing in most organizations that experience breaches [2]. Verification protocols for unusual requests - especially those mimicking IT alerts or supplier communications - can significantly reduce risks [4][5]. Even so, the doubling of email breaches despite existing tools highlights the need for continuous monitoring and stronger identity controls to complement basic email protections [7]. These strategies lay the groundwork for tackling more targeted phishing attacks, which will be explored next.
2. Spear Phishing
Prevalence of the Phishing Type
Spear phishing is a major concern in healthcare because of its highly targeted nature. Suspicious activity accounts for between 2% and 3% of all email and internet traffic in this sector, with healthcare organizations facing over 50 million potentially harmful transactions every year [1]. Alarmingly, 91% of active threat alerts in healthcare are related to credential phishing [1].
Impact on Healthcare Organizations
What makes spear phishing particularly dangerous is its focus on specific individuals or departments. Unlike general phishing, which relies on sending generic emails to a large audience, spear phishing involves highly personalized messages. Attackers often research their targets thoroughly, referencing real colleagues, projects, or events to make their communications seem authentic. This tailored approach exploits the trust inherent in healthcare communications. Adding to the challenge, cybercriminals now use AI to create lifelike profile photos, forged IDs, and even deepfakes, making these attacks nearly impossible to distinguish from legitimate interactions.
Potential for Data Breaches or Financial Loss
The consequences of a successful spear phishing attack in healthcare can be devastating. Medical records, which hold far more value on the black market than credit card information, are prime targets. Once attackers gain access through compromised credentials, they can infiltrate systems housing sensitive patient data. With healthcare's increasing reliance on digital records, human error remains a significant vulnerability. Cybercriminals are also leveraging AI to craft error-free, convincing messages that easily bypass traditional fraud detection systems [1].
Effectiveness of Mitigation Strategies
To counter these advanced threats, healthcare organizations must adopt strong defensive measures. According to Microsoft, using multi-factor authentication (MFA) can reduce the likelihood of a breach by 99% [1]. This ensures that even if credentials are compromised, attackers cannot gain access. A multi-layered email security system is also critical. Combining spam filters, content filters, domain filters, and machine learning tools can help identify and block sophisticated phishing attempts. Regular phishing simulations are another effective strategy, allowing staff to practice spotting and reporting targeted attacks in a safe environment [1].
3. Business Email Compromise (BEC)
Prevalence of the Phishing Type
Business Email Compromise (BEC) is a major threat to healthcare organizations, carrying both financial and reputational risks. According to the FBI's 2023 Internet Crime Report, BEC accounted for $2.9 billion in reported losses from 21,489 complaints [9]. Between October 2013 and December 2022, the Health Sector Cybersecurity Coordination Center (HC3) documented over $50.8 billion in losses from BEC attacks specifically targeting healthcare [9]. While the number of reported incidents slightly dipped in 2023, the financial damage continues to rise. This trend suggests attackers are refining their techniques, making BEC an evolving challenge that demands specialized defenses.
Impact on Healthcare Organizations
BEC attacks exploit trust and familiarity, often using social engineering and compromised email accounts to deceive. Attackers typically pose as trusted figures - such as executives, legal advisors, or vendors - to manipulate organizations into transferring funds or sharing sensitive information. Healthcare is especially vulnerable due to its intricate payment systems, reliance on numerous third-party vendor relationships, and a workforce focused on patient care rather than fraud detection.
For instance, in February 2025, a medical center narrowly avoided losing $500,000 worth of prescription drugs after attackers compromised its DEA ID and pharmaceutical certificates [9]. In another case, criminals targeted a children's hospital by monitoring public announcements about a construction project. They used spoofed domains to impersonate the construction company's CFO, successfully redirecting payments for the project to fraudulent accounts [9].
Potential for Data Breaches or Financial Loss
Beyond financial fraud, BEC attacks can lead to unauthorized access to sensitive patient records and regulatory credentials. Attackers often use cryptocurrency and third-party payment platforms to quickly move stolen funds. Additionally, healthcare's supply chain is a frequent target. Criminals may impersonate medical equipment suppliers or service providers to reroute payments or obtain prescription drugs and construction funds fraudulently.
Effectiveness of Mitigation Strategies
Defending against BEC requires a multi-layered approach. Implementing email authentication protocols like SPF, DKIM, and DMARC can help prevent domain spoofing. Multi-step verification processes, such as confirming vendor payment changes through verified phone calls, are crucial for safeguarding large transactions. Regular access management reviews ensure that employees only have the permissions necessary for their roles, reducing the risk of misuse or exploitation.
Training staff to recognize and challenge suspicious requests - especially those that come with a sense of urgency or authority - is equally important. Employees should feel confident verifying unusual communications, even if they appear to come from high-ranking executives [9].
Healthcare organizations can also benefit from platforms like Censinet RiskOps™ (https://censinet.com), which streamline risk assessments and enhance third-party risk management. Up next, we’ll explore emerging threats like QR Code Phishing.
4. QR Code Phishing
How Common Is This Threat?
QR code phishing, also known as "quishing", is becoming a go-to method for attackers because it can slip past both human awareness and technical defenses. Standard email security systems often don’t decode or analyze QR codes, especially when they’re embedded as images rather than clickable links [10]. This has led to significant financial damage - QR code scams in the U.S. alone have caused $13 million in losses [11]. Beyond digital attacks, criminals place malicious QR codes on physical items like posters, flyers, and stickers, even targeting spaces like healthcare facilities [10].
Why Healthcare Organizations Are at Risk
Healthcare workflows are a prime target for quishing attacks. Malicious QR codes are often disguised in invoices, shipping updates, or account verification prompts, with attackers pretending to represent trusted brands like Microsoft [10]. Some phishing emails use branded images containing embedded QR codes, making them harder to detect through traditional security tools [10]. The Health Sector Cybersecurity Coordination Center (HC3) warns that these attacks could serve as gateways for severe cyberattacks on healthcare organizations [11]. Common tricks include fake requests to update COVID-19 vaccination details, verify insurance information, access patient test results, or review updated medical procedures [11].
Risks of Data Breaches and Financial Damage
QR codes are inherently deceptive because they hide the URLs they lead to, removing a key safety cue for users. When healthcare workers scan these codes, the attack often shifts from secure corporate systems to personal mobile devices, which may not have the same level of security monitoring [10]. These malicious codes can steal login credentials, capture multi-factor authentication tokens, or direct users to malware-infected sites [10]. Unfortunately, curiosity often drives people to scan unknown QR codes, making this attack method especially effective [11]. On the bright side, machine learning tools have shown promise in detecting harmful QR codes, with accuracy rates as high as 96.47% [11].
How to Defend Against Quishing
Protecting against QR code phishing requires targeted strategies. Healthcare organizations should use email security tools capable of decoding QR codes to check their destinations, assess reputations, and analyze redirects [10]. Adding warning banners can discourage staff from scanning external QR codes impulsively [10]. Phishing simulations focused on QR-based lures, such as fake account verifications or invoice prompts, are an excellent way to train employees to spot these scams [10]. Strict policies are also essential - staff should avoid scanning QR codes from unverified sources, especially those demanding immediate action [11]. Regular physical inspections of QR codes in shared spaces, like break rooms or on medical devices, can help detect tampering or unauthorized overlays [11].
For a more robust defense, healthcare organizations can adopt risk management platforms like Censinet's RiskOps™, which simplifies risk assessments and strengthens cybersecurity strategies tailored to the healthcare sector.
Next, we’ll dive into Section 5 to see how AI is making phishing attacks even more sophisticated.
5. AI-Generated Phishing
Prevalence of the Phishing Type
Phishing tactics have taken a sharp turn with the rise of artificial intelligence. Tools like ChatGPT and Google Gemini make it easier than ever for attackers to churn out polished phishing content - no advanced skills required. The result? A staggering 700% increase in credential phishing incidents in late 2024 [12]. This surge is directly tied to generative AI tools, which allow attackers to scale operations like never before. They can tweak tone, formatting, and phrasing on the fly, bypassing security filters and fooling employees with alarming ease. This shift has created a whole new level of risk, particularly for healthcare organizations.
Impact on Healthcare Organizations
Healthcare systems are especially vulnerable to AI-generated phishing. Their sprawling workforces and extensive vendor networks give attackers plenty of opportunities to craft convincing credential requests. Errol Weiss, Chief Security Officer at Health-ISAC, explains the growing threat:
"AI allows attackers to mimic internal IT alerts, HR messages or patient care requests with precision, often using real staff names, logos and organizational language pulled from public sources."
These attacks are designed to steal credentials, allowing hackers to impersonate legitimate users. Traditional firewalls struggle to counter this type of threat. Weiss highlights the core issue:
"The real target in most cyberattacks isn't the system, it's the person logging in."
Once credentials are compromised, it’s not just about stolen data - it’s about opening the door to a series of vulnerabilities across the organization.
Potential for Data Breaches or Financial Loss
AI-generated phishing doesn’t just threaten finances; it puts clinical operations and patient safety at risk. With stolen credentials, attackers gain access to critical systems like Electronic Health Record (EHR) platforms, financial systems, and remote admin tools. This can lead to system outages, unauthorized access to sensitive medical records, and disruptions in patient care. Since attackers can operate under the guise of legitimate users, these breaches often go unnoticed until significant damage is done.
Effectiveness of Mitigation Strategies
Fighting back against AI-generated phishing requires an identity-first approach to security. Here’s how organizations can strengthen their defenses:
Training is another critical piece. Incorporate real-world phishing examples - anonymized but relevant - into clinical workflows to make the threat tangible for staff.
One solution to streamline these efforts is Censinet RiskOps™ (https://censinet.com), which simplifies risk assessments while supporting identity-first security measures.
Comparison Table
Phishing risks come in different forms, each requiring specific strategies to address them effectively. By understanding the nuances of these threats, healthcare organizations can allocate resources wisely and build a multi-layered defense system. Below is a breakdown of five common phishing types, their characteristics, and suggested countermeasures.
Broad attacks with generic messages; often includes basic links or attachments, focusing on volume over precision.
Use standard email filters (spam, domain, content) alongside multifactor authentication (MFA) to thwart unauthorized access, even if credentials are compromised.
Tailored attacks using personal details about the recipient; often references colleagues, projects, or events to build credibility.
Provide role-specific security training with realistic scenarios. Deploy machine learning tools to detect unusual behavior and implement out-of-band verification for sensitive requests.
Mimics executives, vendors, or contractors; often exploits organizational complexities and financial workflows like payment instructions.
Require secondary verification for payment updates, use relationship pattern modeling, and monitor behaviors to detect impersonation attempts.
Embeds malicious QR codes in emails to bypass traditional text-based security filters.
Train employees to manually verify QR codes and conduct regular simulations to improve recognition and reporting of suspicious mobile activities.
Leverages generative AI to create polished, authentic-looking messages that mimic internal communication styles and evade detection.
Use phishing-resistant MFA for high-privilege accounts, AI-driven detection tools, and monitor identity signals like unusual login locations or device changes.
These differences highlight the need for customized email security policies for each threat.
"Understanding what normal behaviors are - if I'm always logging in from Texas, always calling Matt 'Matt,' and all of a sudden I'm calling Matt 'Matthew' and logging in from Hong Kong, well, there's obviously some signals there"
.
Mike Britton, CIO at Abnormal AI, emphasizes the value of monitoring behavioral patterns to identify potential threats.
The healthcare sector remains the most expensive industry for breach costs, averaging $9.77 million per incident - a title it has held for over a decade [13]. Alarmingly, malicious emails bypassing secure email gateways rose by 84.5% in 2024 [1]. Even basic measures like phishing-resistant MFA can reduce breach risks by 99% [1], proving their importance.
For healthcare organizations seeking to strengthen their defenses, solutions like Censinet RiskOps™ provide tailored tools to address the unique challenges of the industry.
This comparison underscores the critical role of targeted, layered defenses in mitigating phishing risks effectively.
Conclusion
Phishing threats, ranging from generic attempts to sophisticated AI-generated schemes, highlight the pressing need for a robust email security strategy. These attacks are the most expensive threat to healthcare email systems, with the average cost of a breach reaching $7.4 million per incident in 2025 - a figure that has more than doubled in recent years [3][7]. Email security can no longer be treated as an afterthought.
To address these risks, healthcare organizations must adopt layered defenses. While employee training is important, the fast-paced healthcare environment requires solutions that intercept phishing attempts before they reach inboxes [4]. This means implementing email-layer security capable of detecting and blocking phishing, impersonation, and spoofed identities at the source [3]. Shockingly, 74% of breached domains in 2025 lacked proper DMARC protection, showing that even basic technical measures are often overlooked [2].
Advanced threat detection is another critical layer. Attackers are increasingly abusing trusted platforms and leveraging AI to craft phishing emails that evade traditional defenses [3][6]. Once credentials are compromised, conventional security measures often fail to identify account takeovers, leaving organizations vulnerable to further damage [3].
Solutions like Censinet RiskOps™ (https://censinet.com) offer targeted protection by managing cybersecurity risks across both internal systems and third-party vendor risk management. This is especially crucial since nearly one-third of email-related incidents involve vendor or business associate exposure [3]. To safeguard patient data in an ever-evolving threat landscape, healthcare organizations must treat email security as essential infrastructure. This involves updating policies, enforcing DMARC, and combining realistic training with advanced technical controls to defend against phishing threats effectively.
FAQs
What’s the fastest way to tell if an email is a phishing attempt in a hospital setting?
Phishing emails can be a real headache, especially in a hospital setting where sensitive information is at stake. To spot one quickly, hover over any links to see where they actually lead - this can reveal suspicious or mismatched URLs. Keep an eye out for red flags, like strange sender addresses or emails that demand urgent action. These tactics are often used to pressure you into making a mistake.
When in doubt, double-check any requests through trusted channels - whether that’s a direct call to the supposed sender or consulting your IT department. Staying alert and following your hospital’s security protocols can go a long way in keeping everyone safe.
Which accounts should get phishing-resistant MFA first?
Phishing-resistant MFA should be prioritized for accounts with privileged or administrative access to critical systems like cloud management consoles, electronic health records (EHRs), and databases. It’s equally important to apply it to secure workforce access to internal tools, including email and web applications, as well as third-party or vendor access to systems that manage electronic protected health information (ePHI).
How can we reduce third-party and vendor email phishing risk?
Healthcare organizations can better protect themselves from phishing attacks by blending technical defenses with effective staff training. Here’s how:
Adding regular phishing simulations to your training program can help employees stay alert. Combine this with a solid incident response plan to reduce vulnerabilities and tighten email security.
Related Blog Posts
- Checklist for Identifying Phishing Emails in Healthcare
- How to Secure Email Gateways in Healthcare
- AI-Enhanced Phishing: The Evolution of Social Engineering Attacks
- AI in Phishing Response: Healthcare Use Cases
{"@context":"https://schema.org","@type":"FAQPage","mainEntity":[{"@type":"Question","name":"What’s the fastest way to tell if an email is a phishing attempt in a hospital setting?","acceptedAnswer":{"@type":"Answer","text":"<p>Phishing emails can be a real headache, especially in a hospital setting where sensitive information is at stake. To spot one quickly, <strong>hover over any links</strong> to see where they actually lead - this can reveal suspicious or mismatched URLs. Keep an eye out for <strong>red flags</strong>, like strange sender addresses or emails that demand urgent action. These tactics are often used to pressure you into making a mistake.</p> <p>When in doubt, <strong>double-check any requests through trusted channels</strong> - whether that’s a direct call to the supposed sender or consulting your IT department. Staying alert and following your hospital’s security protocols can go a long way in keeping everyone safe.</p>"}},{"@type":"Question","name":"Which accounts should get phishing-resistant MFA first?","acceptedAnswer":{"@type":"Answer","text":"<p>Phishing-resistant MFA should be prioritized for accounts with <strong>privileged or administrative access</strong> to critical systems like cloud management consoles, electronic health records (EHRs), and databases. It’s equally important to apply it to secure <strong>workforce access</strong> to internal tools, including email and web applications, as well as <strong>third-party or vendor access</strong> to systems that manage electronic protected health information (ePHI).</p>"}},{"@type":"Question","name":"How can we reduce third-party and vendor email phishing risk?","acceptedAnswer":{"@type":"Answer","text":"<p>Healthcare organizations can better protect themselves from phishing attacks by blending technical defenses with effective staff training. Here’s how:</p> <ul> <li><strong>Implement secure email protocols</strong>: Use tools like encryption, data loss prevention (DLP), and multi-factor authentication (MFA) to safeguard sensitive communications.</li> <li><strong>Train employees</strong>: Teach staff how to spot phishing attempts, verify requests through trusted channels, and steer clear of suspicious links or attachments.</li> </ul> <p>Adding regular phishing simulations to your training program can help employees stay alert. Combine this with a solid incident response plan to reduce vulnerabilities and tighten email security.</p>"}}]}
Key Points:
Why is phishing the most significant cybersecurity threat facing healthcare email systems?
- Phishing is the entry point for more than 90% of healthcare cyberattacks, making it the single most consequential threat vector for an industry that handles some of the most sensitive and valuable data in any sector
- The average cost of a phishing-related breach in healthcare reached $7.4 million per incident in 2025, a figure that has more than doubled in recent years and continues to rise as attack sophistication increases
- Healthcare holds the most expensive breach cost of any industry at $9.77 million per incident, a position it has held for over a decade, reflecting both the value of medical records on criminal markets and the operational complexity of recovering compromised clinical systems
- Malicious emails bypassing secure email gateways rose 84.5% in 2024, indicating that traditional perimeter defenses are no longer sufficient and that attackers are successfully adapting their techniques to evade existing security tools
- 41% of healthcare organizations were categorized as high risk in 2025, up from 31% the prior year, reflecting a deteriorating email security posture across the sector despite increased investment in cybersecurity
- Nearly one-third of email-related incidents involve vendor or business associate exposure, making third-party email security risk a material component of healthcare organizations' overall phishing threat surface
What are the defining characteristics and risks of general email phishing in healthcare?
- General email phishing accounted for 63% of healthcare email-related breaches in 2025 and remains the foundational attack method from which more sophisticated techniques are built, exploiting the high volume of email communications in clinical and administrative workflows
- Mailbox takeovers caused by phishing exposed over 630,000 patient records in 2025, with attackers using stolen credentials to log in undetected and systematically harvest protected health information from historical email archives
- 74% of healthcare domains that experienced breaches lacked proper DMARC protection, enabling attackers to spoof trusted email addresses and send messages that appear to originate from legitimate organizational domains
- Microsoft 365 breaches rose to 53% of healthcare email incidents in 2025, up from 43% in 2024, reflecting the concentration of healthcare email in a single platform and the corresponding concentration of attacker focus on that environment
- High-pressure tactics such as fake IT alerts and supplier requests are the primary social engineering mechanisms used in general phishing, designed to create urgency that overrides the recipient's natural skepticism and drives clicks before the message is scrutinized
- Traditional user awareness training is insufficient once credentials are stolen, because a trained employee who has already been compromised cannot undo the damage, requiring email-layer security that blocks phishing attempts before they reach inboxes as the primary defense
How do spear phishing and business email compromise differ in their approach and what defenses address each?
- Spear phishing uses personal research to craft targeted messages that reference real colleagues, active projects, and organizational events, making them indistinguishable from legitimate communications to recipients who are not specifically trained to recognize the pattern
- AI tools now enable attackers to create lifelike profile photos, forged IDs, and deepfakes that accompany spear phishing messages, raising the level of social proof beyond what traditional awareness training prepares employees to evaluate
- Business email compromise is a financially motivated variant that impersonates executives, vendors, or legal advisors specifically to redirect payments or obtain sensitive credentials, with the FBI's 2023 Internet Crime Report attributing $2.9 billion in reported losses to this attack type
- Healthcare's BEC exposure is amplified by its financial complexity, including pharmaceutical procurement, construction project payments, and insurance reimbursement workflows, all of which involve large-dollar transactions and multiple vendor relationships that attackers study and exploit
- Multi-factor authentication reduces breach likelihood by 99% according to Microsoft research and is the single most effective technical control against both spear phishing credential theft and BEC account compromise
- Secondary verification for payment changes through confirmed out-of-band communication is the operational control that most directly addresses BEC risk, requiring that any request to redirect funds or change vendor payment details be confirmed through a verified phone call to a known contact rather than a reply to the suspicious email
What is QR code phishing and why does it pose a specific risk to healthcare organizations?
- QR code phishing embeds malicious QR codes in emails as images, bypassing standard email security tools that analyze text-based URLs but cannot decode or assess the destination of a QR code rendered as an image attachment
- The attack shifts the threat from corporate email systems to personal mobile devices when healthcare workers scan QR codes on their phones, moving the interaction to devices that may lack the monitoring and security controls applied to corporate endpoints
- QR codes are inherently deceptive because they hide the URLs they contain, removing the ability of even cautious recipients to assess a link before following it, which eliminates one of the primary behaviors that phishing awareness training teaches
- Common healthcare-specific QR phishing lures include fake requests to update COVID-19 vaccination details, verify insurance information, access patient test results, and review updated medical procedures, exploiting the clinical and administrative workflows that healthcare workers engage with regularly
- The Health Sector Cybersecurity Coordination Center has warned that QR phishing attacks can serve as gateways to more severe cyberattacks on healthcare organizations, including ransomware deployments and EHR system compromise following credential capture
- Machine learning tools for QR code analysis have demonstrated accuracy rates as high as 96.47% in detecting malicious QR codes, and email security platforms with QR decoding capability represent the primary technical control for organizations seeking to close this defensive gap
How is AI changing the phishing threat landscape for healthcare and what controls are most effective against AI-generated attacks?
- Generative AI tools enabled a 700% increase in credential phishing incidents in late 2024, driven by the ability of attackers to produce high-quality phishing content at scale without the writing skills, language fluency, or template development previously required
- AI-generated phishing can precisely mimic internal IT alerts, HR messages, and patient care requests using real staff names, logos, and organizational language harvested from public sources, making these messages exceptionally difficult to identify through content analysis alone
- The primary target of AI-generated phishing is credentials rather than data directly, with attackers using stolen logins to impersonate legitimate users, access EHR platforms and financial systems, and operate undetected within compromised accounts for extended periods
- Phishing-resistant MFA for high-privilege accounts is the most critical technical control against AI-generated phishing, because even a perfectly convincing message cannot result in system access if the authentication mechanism cannot be satisfied with stolen credentials alone
- Behavioral monitoring that flags unusual login patterns such as access from unfamiliar devices, multiple geographic locations, or atypical hours provides the detection capability needed to identify account takeovers that have already occurred despite other controls
- Routine directory audits to deactivate old or unused accounts reduce the attack surface available for AI-generated phishing campaigns by eliminating dormant credentials that can be compromised without triggering activity-based alerts
What layered defense strategy should healthcare organizations implement to address all five phishing risk types?
- Email-layer security that intercepts phishing attempts before they reach inboxes is the foundational control, as user awareness training alone cannot compensate for the volume and sophistication of current attacks once a credential is stolen or a link is clicked
- DMARC enforcement is a basic technical requirement that 74% of breached healthcare organizations had not implemented in 2025, making it one of the highest-priority gap closures for organizations that have not yet deployed email authentication protocols including SPF, DKIM, and DMARC
- Role-specific phishing simulation training using realistic, anonymized real-world examples is more effective than generic awareness programs because it prepares employees for the specific lures and social engineering patterns relevant to their clinical or administrative role
- QR code decoding capability in email security tools, combined with warning banners on external QR codes, addresses the specific technical gap that allows quishing attacks to bypass standard email filters
- Third-party and vendor email phishing risk requires dedicated controls including vendor-specific MFA requirements, monitoring of vendor email access patterns, and integration of vendor risk assessments that evaluate email security posture alongside other cybersecurity controls
- Censinet RiskOps supports a comprehensive phishing defense strategy by managing cybersecurity risks across internal systems and third-party vendor relationships, providing the vendor risk visibility needed to address the nearly one-third of healthcare email incidents that involve business associate or vendor exposure


